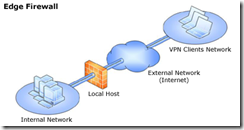
If you have roaming users who want to access internal/private network but you don’t want to spend money at all. Your existing infrastructure consist of Microsoft AD, DNS, DHCP and ISA as firewall. Same as the picture below. Well, you don’t need to spend money to accomplish this objective. It’s few mouse click away.
Figure: Microsoft ISA Edge Firewall, source: Microsoft Corp.
As I mention above, you need MS AD, DNS, DHCP, Active Directory Certificate Services and ISA server. If you don’t have certificate server, you can vertualize it following this instruction. Now you have to do following steps:
- Check DNS, DHCP and AD connectivity in ISA server, make sure it is functioning properly.
- Check/ping public IP configured in one of the NICs in ISA server (ISA got at least two NICs, internal-private IP and external-public IP)
- Create a specific group in AD and add users who want VPN access
- Install machine/computer certificate in ISA server
- Configure VPN in ISA server
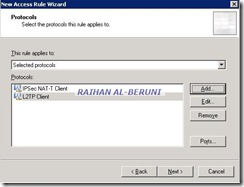
- Create L2TP client access policy
- Install user and machine certificates in VPN client machine
- Create L2TP VPN dialler in client machine and test connection
The following the screen shots will definitely be helpful for you.
ISA Management console>VPN>VPN Property
ISA Management Console>VPN>VPN Clients property
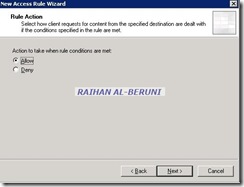
ISA management Console>Firewall Policy>Create New Access Policy
ISA Management Console>Apply.
Further Study:
Administrator’s Guide to Microsoft L2TP/IPSec VPN Client
Keywords: ISA Server, L2TP IPSec, VPN